Safeguarding Your Business: Understanding and Preventing Business Email Compromise (BEC)
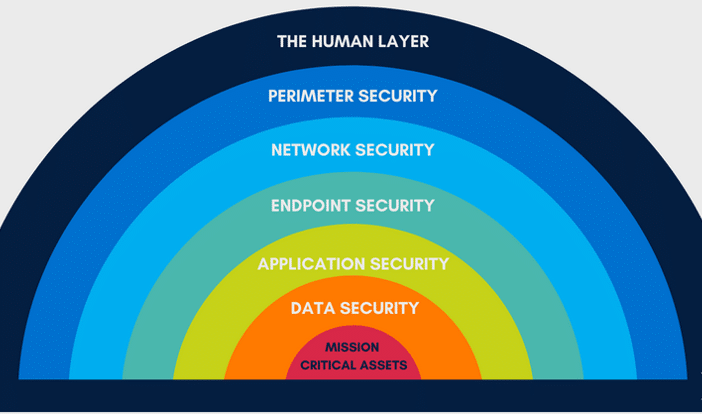
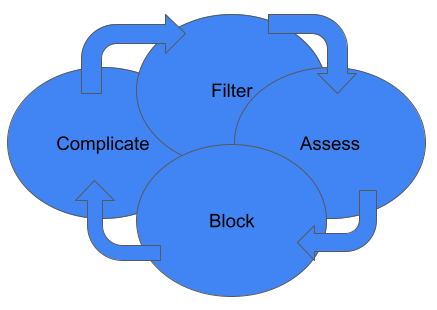
In today\’s digital age, businesses face a myriad of cybersecurity threats, and one of the most prevalent and damaging is Business Email Compromise (BEC). BEC attacks have become increasingly sophisticated, targeting businesses of all sizes and industries. Understanding the causes, techniques, and prevention methods of BEC is crucial for safeguarding your organization\’s sensitive information and […]
Safeguarding Your Business: Understanding and Preventing Business Email Compromise (BEC) Read More »